
我们不仅可以通过相应工具识别目标主机上的服务指纹信息,还可以进行系统指纹信息识别。常见的系统指纹信息有操作系统类型、系统版本和内核版本等。本文介绍系统识别的方法。
1. Nmap系统识别
在Nmap工具中,提供了一些选项可以用来实施系统识别。下面介绍具体的实现方法。
(1)识别操作系统
在Nmap工具中提供了一个-O选项,可以用来识别操作系统。用于识别操作系统的语法格式如下:
nmap -O [host]
其中,-O选项用于识别操作系统类型。注意,这里的选项-O是大写字母O,不是0。
识别目标主机192.168.33.152的操作系统类型。执行命令如下:
root@daxueba:~#nmap-O192.168.33.152 StartingNmap7.70(https://nmap.org)at2021-08-0215:22CST Nmapscanreportfor192.168.33.152(192.168.33.152) Hostisup(0.00036slatency). Notshown:997closedports PORTSTATESERVICE 21/tcpopenftp 22/tcpopenssh 80/tcpopenhttp MACAddress:00:0C:29:FD:58:4B(VMware)#MAC地址 Devicetype:generalpurpose#设备类型 Running:Linux3.X|4.X#运行的系统 OSCPE:cpe:/o:linux:linux_kernel:3cpe:/o:linux:linux_kernel:4#操作系统中央处理单元 OSdetails:Linux3.2-4.9#操作系统详细信息 NetworkDistance:1hop#网络距离,即从源到目标经过的网络节点 OSdetectionperformed.Pleasereportanyincorrectresultsathttps://nmap. org/submit/. Nmapdone:1IPaddress(1hostup)scannedin1.86seconds
从以上输出信息中可以看到,目标主机的操作系统类型为Linux,内核版本为3.2。如果Nmap不能够判断出目标操作系统的话,将会提供指纹信息给Nmap的系统数据库。例如,识别目标主机10.10.1.11的操作系统。执行命令如下:
root@daxueba:~#nmap-O10.10.1.11 StartingNmap7.70(https://nmap.org)at2021-08-0215:29CST …… NoexactOSmatchesforhost(IfyouknowwhatOSisrunningonit,seehttp://nmap.org/submit/). TCP/IPfingerprint: OS:SCAN(V=5.00%D=12/16%OT=3001%CT=1%CU=32781%PV=Y%DS=1%G=Y%M=00204A%TM=4B29 OS:4048%P=i686-pc-windows-windows)SEQ(CI=I%III=I%TS=U)OPS(O1=M400%O2=%O3=%O4 OS:=%O5=%O6=)OPS(O1=M400%O2=M400%O3=%O4=%O5=%O6=)OPS(O1=%O2=M400%O3=M400%O4 OS:=%O5=%O6=)OPS(O1=%O2=%O3=M400%O4=%O5=%O6=)OPS(O1=M400%O2=%O3=M400%O4=%O5 OS:=%O6=)WIN(W1=7FF%W2=0%W3=0%W4=0%W5=0%W6=0)WIN(W1=7FF%W2=7FF%W3=0%W4=0%W5 OS:=0%W6=0)WIN(W1=0%W2=7FF%W3=7FF%W4=0%W5=0%W6=0)WIN(W1=0%W2=0%W3=7FF%W4=0% OS:W5=0%W6=0)WIN(W1=7FF%W2=0%W3=7FF%W4=0%W5=0%W6=0)ECN(R=Y%DF=Y%T=40%W=0%O= OS:%CC=N%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=)T1(R=Y%DF=Y%T=40%S=O%A=O OS:%F=AS%RD=0%Q=)T1(R=Y%DF=Y%T=40%S=Z%A=S+%F=AR%RD=0%Q=)T2(R=Y%DF=Y%T=40%W= OS:0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q= OS:)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T=40%W=0%S=Z%A= OS:S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF OS:=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=Y%T=40%IPL=38%UN=0%RIPL=G OS:%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=S%T=40%CD=S)
以上输出信息就是Nmap向数据库提交的指纹信息,这些指纹信息是自动生成的,并且标识了目标系统的操作系统。
(2)指定识别的操作系统
当扫描多个主机时,可以使用–osscan-limit选项来指定识别特定主机的操作系统类型。这样,使用该选项进行操作系统识别可以节约大量的时间。指定识别主机的操作系统类型语法格式如下:
nmap-O--osscan-limit[host]
其中,–osscan-limit选项表示针对指定的目标进行操作系统检测。如果发现一个打开和关闭的TCP端口时,操作系统检测会更有效。使用该选项,Nmap只对满足这个条件的主机进行操作系统检测。这样可以节约时间,特别是在使用-P0扫描多个主机时。该选项仅在使用-O或-A进行操作系统检测时起作用。
使用Nmap针对指定的目标进行操作系统检测。执行命令如下:
root@daxueba:~#nmap-P0192.168.1.0/24-O--osscan-limit StartingNmap7.70(https://nmap.org)at2021-08-0216:02CST Nmapscanreportfor192.168.1.1(192.168.1.1) Hostisup(0.00073slatency). Notshown:994closedports PORTSTATESERVICE 21/tcpopenftp 80/tcpopenhttp 445/tcpopenmicrosoft-ds 5678/tcpopenrrac 8080/tcpopenhttp-proxy 52869/tcpopenunknown MACAddress:70:85:40:53:E0:35(Unknown) Devicetype:generalpurpose Running:Linux3.X|4.X OSCPE:cpe:/o:linux:linux_kernel:3cpe:/o:linux:linux_kernel:4 OSdetails:Linux3.2-4.9#操作系统详细信息 NetworkDistance:1hop Nmapscanreportforkdkdahjd61y369j(192.168.1.3) Hostisup(0.000085slatency). All1000scannedportsonkdkdahjd61y369j(192.168.1.3)arefiltered MACAddress:1C:6F:65:C8:4C:89(Giga-byteTechnology) Nmapscanreportfortest-pc(192.168.1.5) Hostisup(0.00047slatency). Notshown:982closedports PORTSTATESERVICE 21/tcpopenftp 22/tcpopenssh 80/tcpopenhttp 135/tcpopenmsrpc 139/tcpopennetbios-ssn 443/tcpopenhttps 445/tcpopenmicrosoft-ds 902/tcpopeniss-realsecure 912/tcpopenapex-mesh 1433/tcpopenms-sql-s 2383/tcpopenms-olap4 5357/tcpopenwsdapi 49152/tcpopenunknown 49153/tcpopenunknown 49154/tcpopenunknown 49155/tcpopenunknown 49157/tcpopenunknown 49158/tcpopenunknown MACAddress:00:0C:29:21:8C:96(VMware) Devicetype:generalpurpose Running:MicrosoftWindows7|2008|8.1 OSCPE:cpe:/o:microsoft:windows_7::-cpe:/o:microsoft:windows_7::sp1 cpe:/o:microsoft:windows_server_2008::sp1cpe:/o:microsoft:windows_server_ 2008:r2cpe:/o:microsoft:windows_8cpe:/o:microsoft:windows_8.1 OSdetails:MicrosoftWindows7SP0-SP1,WindowsServer2008SP1,Windows Server2008R2,Windows8,orWindows8.1Update1#操作系统详细信息 NetworkDistance:1hop Nmapscanreportfor192.168.1.6(192.168.1.6) Hostisup(0.00057slatency). Notshown:977closedports PORTSTATESERVICE 21/tcpopenftp 22/tcpopenssh 23/tcpopentelnet 25/tcpopensmtp 53/tcpopendomain 80/tcpopenhttp 111/tcpopenrpcbind 139/tcpopennetbios-ssn 445/tcpopenmicrosoft-ds 512/tcpopenexec 513/tcpopenlogin 514/tcpopenshell 1099/tcpopenrmiregistry 1524/tcpopeningreslock 2049/tcpopennfs 2121/tcpopenccproxy-ftp 3306/tcpopenmysql 5432/tcpopenpostgresql 5900/tcpopenvnc 6000/tcpopenX11 6667/tcpopenirc 8009/tcpopenajp13 8180/tcpopenunknown MACAddress:00:0C:29:3E:84:91(VMware) Devicetype:generalpurpose Running:Linux2.6.X OSCPE:cpe:/o:linux:linux_kernel:2.6 OSdetails:Linux2.6.9-2.6.33#操作系统详细信息 NetworkDistance:1hop Nmapscanreportforkali(192.168.1.9) Hostisup(0.00093slatency). All1000scannedportsonkali(192.168.1.9)areclosed MACAddress:00:0C:29:6C:C4:92(VMware) Nmapscanreportfordaxueba(192.168.1.4) Hostisup(0.000010slatency). All1000scannedportsondaxueba(192.168.1.4)areclosed OSdetectionperformed.Pleasereportanyincorrectresultsat https://nmap.org/submit/. Nmapdone:256IPaddresses(6hostsup)scannedin7.64seconds
从以上输出信息可以看到,如果探测到目标主机上存在开放的端口,则推测出了其操作系统类型;如果目标主机上不存在开放的端口,则无法推测其操作系统类型。
(3)推测操作系统
当Nmap无法确定所探测的操作系统时,会尽可能地提供最相近的匹配。为了对目标系统推测得更准确,可以使用–osscan-guess或–fuzzy选项来实现。语法格式如下:
nmap-O--osscan-guess;--fuzzy[host]
其中,–osscan-guess;–fuzzy选项用于推测操作系统检测结果,将以百分比的方式给出对操作系统信息的猜测。当Nmap无法确定所检测的操作系统时,会尽可能地提供最相近的匹配。Nmap默认进行这种匹配,使用任意一个选项将使得Nmap的推测更加有效。
推测目标主机www.163.com的操作系统类型。执行命令如下:
root@daxueba:~#nmap-O--osscan-guesswww.163.com StartingNmap7.70(https://nmap.org)at2021-08-0216:08CST Nmapscanreportforwww.163.com(124.163.204.105) Hostisup(0.015slatency). Otheraddressesforwww.163.com(notscanned):2408:8726:5100::4f rDNSrecordfor124.163.204.105:105.204.163.124.in-addr.arpa Notshown:955closedports PORTSTATESERVICE 80/tcpopenhttp 81/tcpopenhosts2-ns 82/tcpopenxfer 84/tcpopenctf 88/tcpopenkerberos-sec 135/tcpfilteredmsrpc 139/tcpfilterednetbios-ssn 443/tcpopenhttps 445/tcpfilteredmicrosoft-ds ……省略部分内容 Devicetype:generalpurpose|firewall|mediadevice|phone|broadbandroutersecurity-misc Running(JUSTGUESSING):Linux3.X|2.6.X|4.X(92%),IPCop2.X(91%),Tiandy embedded(91%),GoogleAndroid5.X(90%),D-Linkembedded(90%),Draytek embedded(89%) OSCPE:cpe:/o:linux:linux_kernel:3.2cpe:/o:linux:linux_kernel:2.6.32 cpe:/o:ipcop:ipcop:2.0cpe:/o:linux:linux_kernel:4.9cpe:/o:google: android:5.0.1cpe:/h:dlink:dsl-2890alcpe:/o:linux:linux_kernel:2.6.25.20 cpe:/h:draytek:vigor_2960 AggressiveOSguesses:Linux3.2(92%),IPCop2.0(Linux2.6.32)(91%),Linux 2.6.32(91%),Linux4.9(91%),TiandyNVR(91%),Android5.0.1(90%),Linux 3.18(90%),D-LinkDSL-2890ALADSLrouter(90%),OpenWrtKamikaze8.09(Linux 2.6.25.20)(90%),Linux2.6.18-2.6.22(89%) NoexactOSmatchesforhost(testconditionsnon-ideal). NetworkDistance:9hops OSdetectionperformed.Pleasereportanyincorrectresultsathttps://nmap.org/submit/. Nmapdone:1IPaddress(1hostup)scannedin5.65seconds
以上输出信息显示了目标主机可能使用的操作系统列表。这里列举可能的系统类型,并以百分比形式显示每种类型的概率。从输出结果显示的比例中可以看到,目标主机的操作系统类型可能是Linux 3.2。
2. Ping系统识别
Ping是Windows、UNIX和Linux系统下的一个命令,使用该命令可以检查网络是否连通。如果目标主机正确响应的话,在响应包中将包括有对应的TTL值。TTL是Time To Live(生成时间)的缩写,该字段指定IP包被路由器丢弃之前允许通过的最大网段数量。其中,不同操作系统类型响应的TTL值不同。所以我们可以使用Ping命令进行系统识别。下面介绍使用Ping命令实施系统识别的方法。
为了能够快速地确定一个目标系统的类型,下面给出了一个操作系统初始TTL值列表,如表1所示。
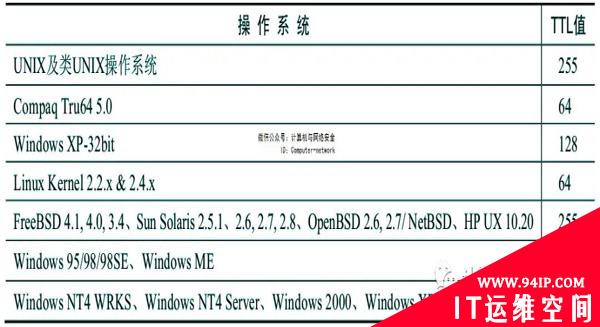
表1 各个操作系统的初始TTL值
使用Ping测试目标主机(192.168.33.152)的操作系统类型(该目标主机的操作系统类型为Linux)。执行命令如下:
root@daxueba:~#ping192.168.33.152 PING192.168.33.152(192.168.33.152)56(84)bytesofdata. 64bytesfrom192.168.33.152:icmp_seq=1ttl=64time=0.242ms 64bytesfrom192.168.33.152:icmp_seq=2ttl=64time=0.431ms 64bytesfrom192.168.33.152:icmp_seq=3ttl=64time=0.431ms 64bytesfrom192.168.33.152:icmp_seq=4ttl=64time=0.440ms
从输出的信息可以看到,响应包中的TTL值为64。根据前面列出的表格6.1,可以看到这是Linux操作系统。
使用Ping测试目标主机(192.168.33.229)的操作系统类型(该目标主机的操作系统类型为Windows 7)。执行命令如下:
root@daxueba:~#ping192.168.33.229 PING192.168.33.229(192.168.33.229)56(84)bytesofdata. 64bytesfrom192.168.33.229:icmp_seq=1ttl=128time=1.57ms 64bytesfrom192.168.33.229:icmp_seq=2ttl=128time=1.01ms 64bytesfrom192.168.33.229:icmp_seq=3ttl=128time=0.276ms 64bytesfrom192.168.33.229:icmp_seq=4ttl=128time=1.52ms
从输出的信息可以看到,该响应包中的TTL值为128。由此可以说明,这是一个Windows操作系统。
3. xProbe2系统识别
xProbe2是一款远程主机操作系统探查工具,该工具通过ICMP协议来获得指纹。xProbe2通过模糊矩阵统计分析主动探测数据报文对应的ICMP数据报特征,进而探测得到远端操作系统的类型。下面介绍使用xProbe2工具实施操作系统指纹识别的方法。使用xProbe2工具实施系统识别的语法格式如下:
xProbe2[host]
使用xProbe2工具对目标主机www.163.com实施系统识别。执行命令如下:
root@Kali:~#xprobe2www.163.com Xprobe2v.0.3Copyright(c)2002-2005fyodor@o0o.nu,ofir@sys-security.com,meder@o0o.nu [+]Targetiswww.163.com#目标地址 [+]Loadingmodules.#正在加载模块 [+]Followingmodulesareloaded:#被加载的模块 [x][1]ping:icmp_ping-ICMPechodiscoverymodule [x][2]ping:tcp_ping-TCP-basedpingdiscoverymodule [x][3]ping:udp_ping-UDP-basedpingdiscoverymodule [x][4]infogather:ttl_calc-TCPandUDPbasedTTLdistancecalculation [x][5]infogather:portscan-TCPandUDPPortScanner [x][6]fingerprint:icmp_echo-ICMPEchorequestfingerprintingmodule [x][7]fingerprint:icmp_tstamp-ICMPTimestamprequestfingerprintingmodule [x][8]fingerprint:icmp_amask-ICMPAddressmaskrequestfingerprintingmodule [x][9]fingerprint:icmp_port_unreach-ICMPportunreachablefingerprintingmodule [x][10]fingerprint:tcp_hshake-TCPHandshakefingerprintingmodule [x][11]fingerprint:tcp_rst-TCPRSTfingerprintingmodule [x][12]fingerprint:smb-SMBfingerprintingmodule [x][13]fingerprint:snmp-SNMPv2cfingerprintingmodule [+]13modulesregistered [+]Initializingscanengine#初始化扫描引擎 [+]Runningscanengine#正在实施扫描 [-]ping:tcp_pingmodule:noclosed/openTCPportsknownon124.163.204.105. Moduletestfailed [-]ping:udp_pingmodule:noclosed/openUDPportsknownon124.163.204.105. Moduletestfailed [-]Nodistancecalculation.124.163.204.105appearstobedeadornoportsknown [+]Host:124.163.204.105isup(Guessprobability:50%)#主机是活动的 [+]Target:124.163.204.105isalive.Round-TripTime:0.01503sec [+]SelectedsafeRound-TripTimevalueis:0.03007sec [-]fingerprint:tcp_hshakeModuleexecutionaborted(noopenTCPportsknown) [-]fingerprint:smbneedeitherTCPport139or445torun [-]fingerprint:snmp:needUDPport161open [+]Primaryguess:#主要猜测 [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.19"(Guess probability:100%) [+]Otherguesses:#其他猜测 [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.20"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.21"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.22"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.23"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.24"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.25"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.26"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.27"(Guess probability:100%) [+]Host124.163.204.105RunningOS:"LinuxKernel2.4.28"(Guess probability:100%) [+]Cleaningupscanengine [+]Modulesdeinitialized [+]Executioncompleted.
从输出的信息中可以看到,通过xProbe2工具成功解析出了目标主机的IP地址,并且识别出了其操作系统类型。其中,目标主机的IP地址为124.163.204.105,操作系统类型为Linux,内核版本在2.4.19~2.4.28之间。
xProbe2工具在NAT模式下存在Bug,扫描后会出现HP的位置或者直接报错,具体如下:
root@Kali:~#xprobe2www.163.com Xprobe2v.0.3Copyright(c)2002-2005fyodor@o0o.nu,ofir@sys-security.com,meder@o0o.nu [+]Targetiswww.163.com [+]Loadingmodules. [+]Followingmodulesareloaded: [x][1]ping:icmp_ping-ICMPechodiscoverymodule [x][2]ping:tcp_ping-TCP-basedpingdiscoverymodule [x][3]ping:udp_ping-UDP-basedpingdiscoverymodule [x][4]infogather:ttl_calc-TCPandUDPbasedTTLdistancecalculation [x][5]infogather:portscan-TCPandUDPPortScanner [x][6]fingerprint:icmp_echo-ICMPEchorequestfingerprintingmodule [x][7]fingerprint:icmp_tstamp-ICMPTimestamprequestfingerprintingmodule [x][8]fingerprint:icmp_amask-ICMPAddressmaskrequestfingerprintingmodule [x][9]fingerprint:icmp_port_unreach-ICMPportunreachable fingerprintingmodule [x][10]fingerprint:tcp_hshake-TCPHandshakefingerprintingmodule [x][11]fingerprint:tcp_rst-TCPRSTfingerprintingmodule [x][12]fingerprint:smb-SMBfingerprintingmodule [x][13]fingerprint:snmp-SNMPv2cfingerprintingmodule [+]13modulesregistered [+]Initializingscanengine [+]Runningscanengine [-]ping:tcp_pingmodule:noclosed/openTCPportsknownon124.163.204.105. Moduletestfailed [-]ping:udp_pingmodule:noclosed/openUDPportsknownon124.163.204.105. Moduletestfailed [-]Nodistancecalculation.124.163.204.105appearstobedeadornoportsknown [+]Host:124.163.204.105isup(Guessprobability:50%) [+]Target:124.163.204.105isalive.Round-TripTime:0.01528sec [+]SelectedsafeRound-TripTimevalueis:0.03056sec [-]fingerprint:tcp_hshakeModuleexecutionaborted(noopenTCPportsknown) [-]fingerprint:smbneedeitherTCPport139or445torun [-]fingerprint:snmp:needUDPport161open [+]Primaryguess: [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.07.02EEPROMG.07.17"(Guessprobability:83%) [+]Otherguesses: [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.07.02EEPROMG.07.20"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.07.02EEPROMG.08.04"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.07.19EEPROMG.07.20"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.07.19EEPROMG.08.03"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.07.19EEPROMG.08.04"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.08.08EEPROMG.08.04"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.08.21EEPROMG.08.21"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMH.07.15EEPROMH.08.20"(Guessprobability:83%) [+]Host124.163.204.105RunningOS:"HPJetDirectROMG.06.00EEPROMG.06.00"(Guessprobability:83%) [+]Cleaningupscanengine [+]Modulesdeinitialized [+]Executioncompleted.
从以上输出的信息中可以看到,执行结果出错了(HP JetDirect ROM G.07.02 EEPROM G.07.17)。
在Kali Linux的新版本中,xProbe2工具运行后,测试的结果中操作系统类型显示为乱码。具体如下:
[+]Primaryguess: [+]Host192.168.1.8RunningOS:????U(Guessprobability:100%) [+]Otherguesses: [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Host192.168.1.8RunningOS:?????U(Guessprobability:100%) [+]Cleaningupscanengine [+]Modulesdeinitialized [+]Executioncompleted.
4. p0f系统识别
p0f是一款用于识别远程操作系统的工具,该工具与前面介绍的其他工具不同,它是一个完全被动地识别操作系统指纹信息的工具,不会直接作用于目标系统。当启动该工具后,即可监听网络中的所有数据包。通过分析监听到的数据包,即可找出与系统相关的信息。下面介绍使用p0f工具来实施操作系统指纹识别的方法。
使用p0f工具对目标主机实施系统识别。执行命令如下:
1)启动p0f工具。执行命令如下:
root@daxueba:~#p0f ---p0f3.09bbyMichalZalewski<lcamtuf@coredump.cx>--- [+]Closed1filedescriptor. [+]Loaded322signaturesfrom'/etc/p0f/p0f.fp'. [+]Interceptingtrafficondefaultinterface'eth0'. [+]Defaultpacketfilteringconfigured[+VLAN]. [+]Enteredmaineventloop.
从以上输出信息中可以看到,p0f工具仅显示了几行信息,无法捕获到其他信息。但是,p0f会一直处于监听状态。
2)此时,当有其他主机在网络中产生数据流量的话,将会被p0f工具监听到。例如,在另一台主机上通过浏览器访问一个站点,然后返回到p0f所在的终端,将看到如下信息:
.-[192.168.1.4/38934->65.200.22.161/80(httprequest)]-#HTTP请求 |client=192.168.1.4/38934#客户端 |app=Safari5.1-6#应用 |lang=English#语言 |params=dishonest#程序 |raw_sig=1:Host,User-Agent,Accept=[*/*],Accept-Language=[en-US,en;q=0.5],Accept-Encoding=[gzip,deflate],?Cache-Control,Pragma=[no-cache],Connection=[keep-alive]:Accept-Charset,Keep-Alive:Mozilla/5.0(X11;Linuxx86_64;rv:60.0)Gecko/20100101Firefox/60.0#数据内容 ---- .-[192.168.1.4/38934->65.200.22.161/80(uptime)]- |server=65.200.22.161/80#服务器 |uptime=30days0hrs22min(modulo45days)#时间 |raw_freq=1048.46Hz#频率 ---- .-[192.168.1.4/38934->65.200.22.161/80(httpresponse)]- |server=65.200.22.161/80 |app=??? |lang=none |params=none |raw_sig=1:Content-Type,?Content-Length,?Last-Modified,?ETag,Accept-Ranges=[bytes],Server,X-Amz-Cf-Id=[X7nIiIIBBeQOTeLSHRH3U4SM6xDHfgwK1EaKf8bdyemtuUoR8JK9Xg==],?Cache-Control,Date,Connection=[keep-alive]:Keep-Alive:AmazonS3 ---- .-[192.168.1.4/32854->52.27.184.151/443(syn)]- |client=192.168.1.4/32854 |os=Linux3.11andnewer |dist=0 |params=none |raw_sig=4:64+0:0:1460:mss*20,7:mss,sok,ts,nop,ws:df,id+:0 ---- .-[192.168.1.4/32854->52.27.184.151/443(hostchange)]- |client=192.168.1.4/32854 |reason=tstampport |raw_hits=0,1,1,1 ---- .-[192.168.1.4/32854->52.27.184.151/443(mtu)]- |client=192.168.1.4/32854 |link=Ethernetormodem |raw_mtu=1500 ---- .-[192.168.1.4/32856->52.27.184.151/443(syn)]- |client=192.168.1.4/32856 |os=Linux3.11andnewer |dist=0 |params=none |raw_sig=4:64+0:0:1460:mss*20,7:mss,sok,ts,nop,ws:df,id+:0 ----
以上输出的信息,就是执行监听到客户端访问的数据信息。从以上输出的信息可以看到,探测到客户端的操作系统类型为Linux 3.11或更新的内核版本。











发表评论