一、Windows-Exploit-Suggester简介
1. 简介
Windows-Exploit-Suggester是受Linux_Exploit_Suggester的启发而开发的一款提权辅助工具,其官方下载地址:https://github.com/GDSSecurity/Windows-Exploit-Suggester,它是用python开发而成,运行环境是python3.3及以上版本,且必须安装xlrd 库(https://pypi.python.org/pypi/xlrd),其主要功能是通过比对systeminfo生成的文件,从而发现系统是否存在未修复漏洞。
2. 实现原理
Windows-Exploit-Suggester通过下载微软公开漏洞库到本地“生成日期+mssb.xls”文件,然后根据操作系统版本,跟systeminfo生成的文件进行比对。微软公开漏洞库下载地址:
http://www.microsoft.com/en-gb/download/confirmation.aspx?id=36982。同时此工具还会告知用户针对于此漏洞是否有公开的exp和可用的Metasploit模块。
二、使用Windows-Exploit-Suggester
1. 下载Windows-Exploit-Suggester、python3.3以及xlrd
https://www.python.org/ftp/python/3.3.3/python-3.3.3.amd64.msi https://pypi.python.org/packages/42/85/25caf967c2d496067489e0bb32df069a8361e1fd96a7e9f35408e56b3aab/xlrd-1.0.0.tar.gz#md5=9a91b688cd4945477ac28187a54f9a3b https://codeload.github.com/GDSSecurity/Windows-Exploit-Suggester/zip/master
2. 本地安装
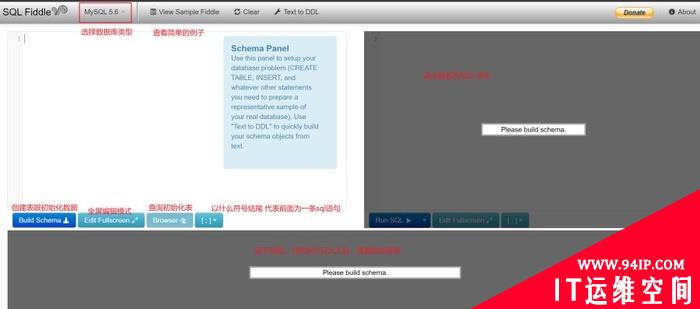
本地安装python3.3.3对应平台版本程序,安装完成后,将文件xlrd-1.0.0.tar.gz复制到python3.3.3安装目录下解压,然后命令提示符下执行setup.py install。否则***次执行会显示无结果,如图1所示,提示升级或者安装xlrd库文件。

图1提示安装xlrd库文件
3. 下载漏洞库
使用以下命令,将在本地文件夹下生成生成日期+mssb.xls”文件,比如使用命令会生成2017-03-20-mssb.xls文件,网上公开资料生成2017-03-20-mssb.xlsx是错误的,如图2所示,执行命令“windows-exploit-suggester.py –update”生成文件2017-03-20-mssb.xls。
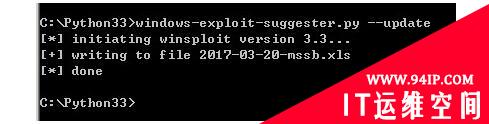
图2生成漏洞库文件
4. 生成系统信息文件
使用“systeminfo > win7sp1-systeminfo.txt”命令生成win7sp1-systeminfo.txt文件,在真实环境中可以将生成的文件下载到本地进行比对。
5. 查看系统漏洞
使用命令“windows-exploit-suggester.py –database 2017-03-20-mssb.xls –systeminfo win7sp1-systeminfo.txt”查看系统存在的高危漏洞,如图3所示,对win7系统进行查看的结果,显示ms14-026为可以利用的PoC。
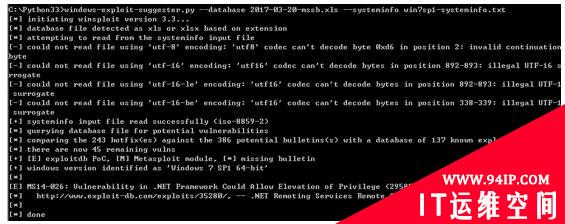
图3查看win7可利用的poc
6. 查看帮助文件
windows-exploit-suggester.py -h查看使用帮助。
三、技巧与高级利用
1. 远程溢出漏洞
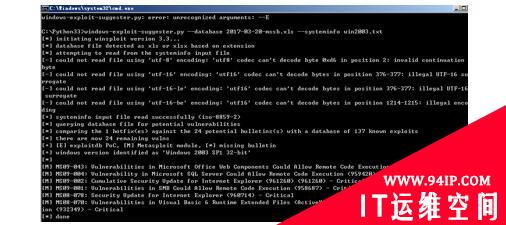
目标系统利用systeminfo生成文件,进行比对,例如对win2003生成的系统信息进行比对:
windows-exploit-suggester.py--database2017-03-20-mssb.xls--systeminfowin2003.txt
结果显示存在MS09-043、MS09-004、MS09-002、MS09-001、MS08-078和MS08-070远程溢出漏洞。
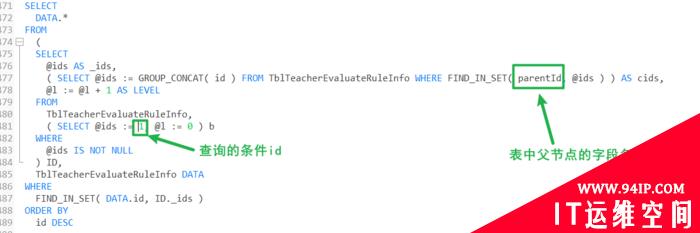
2. 所有漏洞审计
使用以下命令进行所有漏洞的审计,如图5所示,对windows2003 服务器进行审计发现存在24个漏洞。“–audit -l”对本地溢出漏洞进行审计,“–audit -r”对远程溢出漏洞进行审计。
windows-exploit-suggester.py--audit--database2017-03-20-mssb.xls--systeminfowin2003.txt
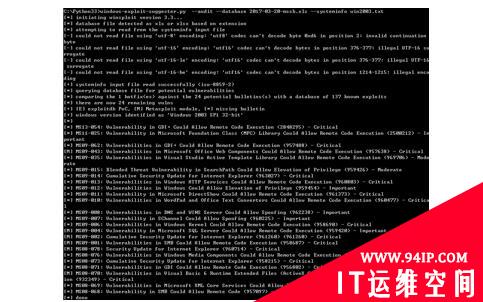
图5审计所有漏洞
3. 搜索本地可利用漏洞信息
“-l”参数比较 78 补丁,137已知漏洞。带“-l”参数搜索本地存在的漏洞命令如下:
windows-exploit-suggester.py--audit-l--database2017-03-20-mssb.xls--systeminfowin2003-2.txt
通过审计本地漏洞发现Windows 2003 server未安装SP2补丁,存在多个本地溢出漏洞,在选择上,选择***的漏洞号进行利用,成功性会高很多,例如在本次实验机上新建一个普通账号temp,登录以后将MS15-077漏洞利用程序进行利用,效果如图6所示。
[*]MS15-077:VulnerabilityinATMFontDriverCouldAllowElevationofPrivilege(3077657)-Important [*]MS15-076:VulnerabilityinWindowsRemoteProcedureCallCouldAllowElevationofPrivilege(3067505)-Important [*]MS15-075:VulnerabilitiesinOLECouldAllowElevationofPrivilege(3072633)-Important [*]MS15-074:VulnerabilityinWindowsInstallerServiceCouldAllowElevationofPrivilege(3072630)-Important [*]MS15-073:VulnerabilitiesinWindowsKernel-ModeDriverCouldAllowElevationofPrivilege(3070102)-Important [*]MS15-072:VulnerabilityinWindowsGraphicsComponentCouldAllowElevationofPrivilege(3069392)-Important [*]MS15-071:VulnerabilityinNetlogonCouldAllowElevationofPrivilege(3068457)-Important [*]MS15-061:VulnerabilitiesinWindowsKernel-ModeDriversCouldAllowElevationofPrivilege(3057839)-Important [M]MS15-051:VulnerabilitiesinWindowsKernel-ModeDriversCouldAllowElevationofPrivilege(3057191)-Important [*]https://github.com/hfiref0x/CVE-2015-1701,Win32kElevationofPrivilegeVulnerability,PoC [*]https://www.exploit-db.com/exploits/37367/--WindowsClientCopyImageWin32kExploit,MSF [*]MS15-050:VulnerabilityinServiceControlManagerCouldAllowElevationofPrivilege(3055642)-Important [*]MS15-048:Vulnerabilitiesin.NETFrameworkCouldAllowElevationofPrivilege(3057134)-Important [*]MS15-038:VulnerabilitiesinMicrosoftWindowsCouldAllowElevationofPrivilege(3045685)-Important [*]MS15-025:VulnerabilitiesinWindowsKernelCouldAllowElevationofPrivilege(3038680)-Important [*]MS15-008:VulnerabilityinWindowsKernel-ModeDriverCouldAllowElevationofPrivilege(3019215)-Important [*]MS15-003:VulnerabilityinWindowsUserProfileServiceCouldAllowElevationofPrivilege(3021674)-Important [*]MS14-078:VulnerabilityinIME(Japanese)CouldAllowElevationofPrivilege(2992719)-Moderate [*]MS14-072:Vulnerabilityin.NETFrameworkCouldAllowElevationofPrivilege(3005210)-Important [E]MS14-070:VulnerabilityinTCP/IPCouldAllowElevationofPrivilege(2989935)-Important [*]http://www.exploit-db.com/exploits/35936/--MicrosoftWindowsServer2003SP2-PrivilegeEscalation,PoC [E]MS14-068:VulnerabilityinKerberosCouldAllowElevationofPrivilege(3011780)-Critical [*]http://www.exploit-db.com/exploits/35474/--WindowsKerberos-ElevationofPrivilege(MS14-068),PoC [*]MS14-063:VulnerabilityinFAT32DiskPartitionDriverCouldAllowElevationofPrivilege(2998579)-Important [M]MS14-062:VulnerabilityinMessageQueuingServiceCouldAllowElevationofPrivilege(2993254)-Important [*]http://www.exploit-db.com/exploits/34112/--MicrosoftWindowsXPSP3MQAC.sys-ArbitraryWritePrivilegeEscalation,PoC [*]http://www.exploit-db.com/exploits/34982/--MicrosoftBluetoothPersonalAreaNetworking(BthPan.sys)PrivilegeEscalation [*]MS14-049:VulnerabilityinWindowsInstallerServiceCouldAllowElevationofPrivilege(2962490)-Important [*]MS14-045:VulnerabilitiesinKernel-ModeDriversCouldAllowElevationofPrivilege(2984615)-Important [E]MS14-040:VulnerabilityinAncillaryFunctionDriver(AFD)CouldAllowElevationofPrivilege(2975684)-Important [*]https://www.exploit-db.com/exploits/39525/--MicrosoftWindows7x64-afd.sysPrivilegeEscalation(MS14-040), [*]https://www.exploit-db.com/exploits/39446/--MicrosoftWindows-afd.sysDanglingPointerPrivilegeEscalation(MS14-040),PoC [E]MS14-026:Vulnerabilityin.NETFrameworkCouldAllowElevationofPrivilege(2958732)-Important [*]http://www.exploit-db.com/exploits/35280/,--.NETRemotingServicesRemoteCommandExecution,PoC [E]MS14-002:VulnerabilityinWindowsKernelCouldAllowElevationofPrivilege(2914368)-Important [*]MS13-102:VulnerabilityinLPCClientorLPCServerCouldAllowElevationofPrivilege(2898715)-Important [*]MS13-062:VulnerabilityinRemoteProcedureCallCouldAllowElevationofPrivilege(2849470)-Important [*]MS13-015:Vulnerabilityin.NETFrameworkCouldAllowElevationofPrivilege(2800277)-Important [*]MS12-042:VulnerabilitiesinWindowsKernelCouldAllowElevationofPrivilege(2711167)-Important [*]MS12-003:VulnerabilityinWindowsClient/ServerRun-timeSubsystemCouldAllowElevationofPrivilege(2646524)-Important [*]MS11-098:VulnerabilityinWindowsKernelCouldallowElevationofPrivilege(2633171)-Important [*]MS11-070:VulnerabilityinWINSCouldAllowElevationofPrivilege(2571621)-Important [*]MS11-051:VulnerabilityinActiveDirectoryCertificateServicesWebEnrollmentCouldAllowElevationofPrivilege(2518295)-Important [E]MS11-011:VulnerabilitiesinWindowsKernelCouldAllowElevationofPrivilege(2393802)-Important [*]MS10-084:VulnerabilityinWindowsLocalProcedureCallCouldCauseElevationofPrivilege(2360937)-Important [*]MS09-041:VulnerabilityinWorkstationServiceCouldAllowElevationofPrivilege(971657)-Important [*]MS09-040:VulnerabilityinMessageQueuingCouldAllowElevationofPrivilege(971032)-Important [M]MS09-020:VulnerabilitiesinInternetInformationServices(IIS)CouldAllowElevationofPrivilege(970483)-Important [*]MS09-015:BlendedThreatVulnerabilityinSearchPathCouldAllowElevationofPrivilege(959426)-Moderate [*]MS09-012:VulnerabilitiesinWindowsCouldAllowElevationofPrivilege(959454)-Important
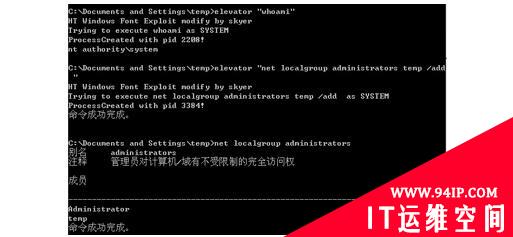
图6利用本地溢出漏洞获取系统权限
4. 查询无补丁信息的可利用漏洞
查询微软漏洞库中所有可用的windows server 2008 r2提权poc信息:
windows-exploit-suggester.py--database2017-03-20-mssb.xls--ostext"windowsserver2008r2"
结果显示如下7所示,主要可利用漏洞信息有:
[M]MS13-009:CumulativeSecurityUpdateforInternetExplorer(2792100)-Critical [M]MS13-005:VulnerabilityinWindowsKernel-ModeDriverCouldAllowElevationofPrivilege(2778930)-Important [E]MS12-037:CumulativeSecurityUpdateforInternetExplorer(2699988)-Critical [*]http://www.exploit-db.com/exploits/35273/--InternetExplorer8-FixedColSpanIDFullASLR,DEP&EMET5.,PoC [*]http://www.exploit-db.com/exploits/34815/--InternetExplorer8-FixedColSpanIDFullASLR,DEP&EMET5.0Bypass(MS12-037),PoC [*][E]MS11-011:VulnerabilitiesinWindowsKernelCouldAllowElevationofPrivilege(2393802)-Important [M]MS10-073:VulnerabilitiesinWindowsKernel-ModeDriversCouldAllowElevationofPrivilege(981957)-Important [M]MS10-061:VulnerabilityinPrintSpoolerServiceCouldAllowRemoteCodeExecution(2347290)-Critical [E]MS10-059:VulnerabilitiesintheTracingFeatureforServicesCouldAllowElevationofPrivilege(982799)-Important [E]MS10-047:VulnerabilitiesinWindowsKernelCouldAllowElevationofPrivilege(981852)-Important [M]MS10-002:CumulativeSecurityUpdateforInternetExplorer(978207)-Critical [M]MS09-072:CumulativeSecurityUpdateforInternetExplorer(976325)-Critical
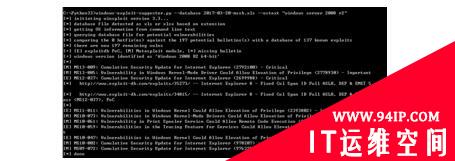
图7 windows 2008 R2可用漏洞
5. 搜索漏洞
根据关键字进行搜索例如MS10-061。
(1)在百度浏览器中搜索“MS10-061 site:exploit-db.com”
(2) packetstormsecurity网站搜索
https://packetstormsecurity.com/search/?q=MS16-016










发表评论